Extending Privileged Access, Everywhere
Delinea Platform
Seamlessly extend Privileged Access Management with the first cloud-native unified PAM platform for just-in-time access with easy, adaptive controls that help IT and security reduce risk while enabling growth, efficiency, and scalability
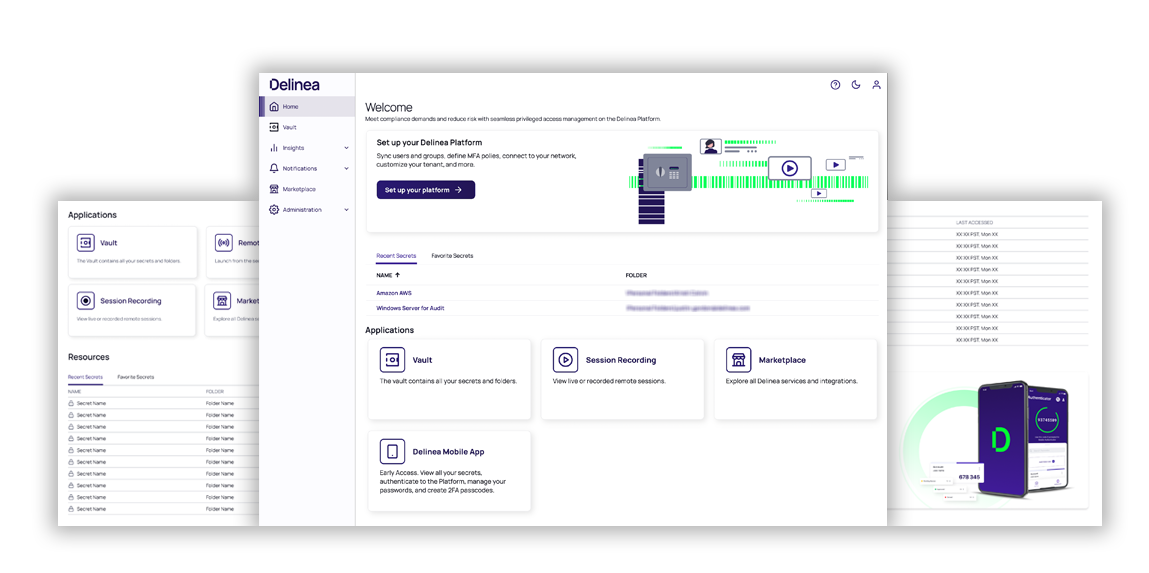
Enterprise-scale Privileged Access Management at lightning speed
End-to-end visibility
Improve visibility across all users, machines, and application privileges while maintaining appropriate security controls.
Dynamic privilege
Manage all privilege authorizations across all types of identities in one solution with consistent policies, even as roles, permissions, and IT resources change.
Adaptive security
Understand identities and assets in context to adjust policies automatically.
See how the Delinea Platform lets you…
Establish an Enterprise Vault
Secure shared credentials that unlock mission-critical enterprise resources. Quickly discover, manage, protect, and audit privileged account access across your organization.
Secure remote access
Grant remote workers and 3rd party vendors VPN-less, agentless browser-based access with applied privileged access policies, a full audit trail, and recorded session activity.
Extend MFA enforcement
Centrally and consistently implement MFA at depth for identity assurance at multiple levels when accessing the vault, a shared credential, at asset login, and privilege elevation.
Seamless integrations with IT and security solutions
Discover and implement tools, templates, and integrations through the Delinea Marketplace to connect PAM to all parts of your IT operations and workflow, security reporting, incident response, and more.
Scale easily
Take advantage of cloud-native security, resiliency, and scalability to grow with your organization’s needs.
Extended PAM helps you save time, avoid mistakes, and lower risk
See why Secret Server customers are extending Privileged Access Management (PAM) to protect hybrid infrastructures, meet compliance requirements, and enable secure remote access. Secret Server on the Delinea Platform eliminates the need to wrangle multiple identity forests to provide the right people with appropriate access. Instead, by providing authorization for all identities and policy-based, adaptive controls, Extended PAM helps you save time, avoid mistakes, and lower risk.
Secure access to privileged credentials with efficiency and scalability
The expansion of the threat landscape has made a secure, ease-to-use enterprise vault critical for every organization. Seamlessly discover, secure, manage, monitor, and audit privileged credentials, allowing teams to align risk mitigation with productivity.
Learn more about Secret Server »
Try Secret Server on the Delinea Platform »

Enforce least privilege best practices on servers
Protect privileged access across Windows, Linux, and Unix servers. Enforce least privilege principles by centralizing authorization controls consistently across identities to help IT and security teams meet compliance, improve productivity, and reduce risk. Build on your enterprise vault by extending Privileged Access Management and layering security directly on your servers using enterprise identities.

Provide instant secure access to remote IT staff and vendors, without a VPN
When your team works remotely or brings in vendors to support a system configuration, maintenance, or troubleshooting, Delinea provides just-in-time, just-enough access. When work ends, access expires automatically, eliminating the danger of standing access.
Learn more about Remote Access Service »
Try Remote Access Service on the Delinea Platform »

Endpoint privilege elevation and application control
Attackers exploit poor security on workstations. Protect against malware and modern security threats by controlling local administrative rights and enforcing least privilege on workstations.

Help IT teams support remote workers so they stay productive
Make it simple for IT teams to configure and secure remote sessions. To support users working remotely, provide IT teams tools to navigate different connection protocols, such as RDP and SSH, inject credentials, and interact with privileged sessions from start to finish.
With Connection Manager, you can connect securely through RDP and SSH and inject privileged credentials into a remote session.

Govern service accounts correctly from the start
Management of service accounts is often neglected since updating or changing credentials without knowing dependencies may affect services. Make sure new service accounts follow PAM best practices.

Manage DevOps privileges with central security controls
DevOps teams need to securely manage and automate access to secrets and credentials at the high speed required by their continuous integration and continuous deployment (CI/CD) workflows. DevOps Secrets Vault (DSV) provides a secure, automated, and centrally managed solution that integrates with DevOps toolchains, allowing teams to manage sensitive data and access secrets across code storage, compilation, testing, and deployment without human intervention.

Leverage shared capabilities across the Delinea Platform to streamline administration while improving operational efficiency and productivity.
The vision for Extended PAM
Redefine PAM to treat all users as privileged users and address complex IT environments.
An edition designed for every type of organization
The flexibility and agility to scale PAM security controls on your own terms
Essentials
Standard
Enterprise
Evolving from PAM to Extended PAM
Introducing the New Delinea Platform
Model for Privileged Access Management Maturity
Solutions for Extended PAM
Full-featured, free trials get you up and running fast
Secret Server
Vault credentials, ensure password complexity, and delegate role-based access.
Server PAM
Centrally manage identities and policies while enforcing least privilege for on-premise and cloud-hosted servers.
Account Lifecycle Manager
Privilege Manager
Remove local admin rights and implement policy-based application control in a single solution.
Privileged Behavior Analytics
Increase accountability and oversight of privileged sessions.
DevOps Secrets Vault
Protect secrets DevOps teams and RPA tools need
